It’s no secret: fleet management software is a key aspect of an efficient and productive fleet. From offering data-driven insights that can help increase your bottom line to helping improve staff safety, there are plenty of benefits that prove the value this technology possesses.
However, as with any valuable tech, it doesn’t come without vulnerabilities to outside threats – including hackers and other forms of cybercrime. Fortunately, with the right software and security measures in place, these concerns can be mitigated.
In this article, we’ll cover the importance of keeping your fleet data safe and what to consider when ensuring your technology is protected against threats.
The Importance of Protecting Your Fleet Data
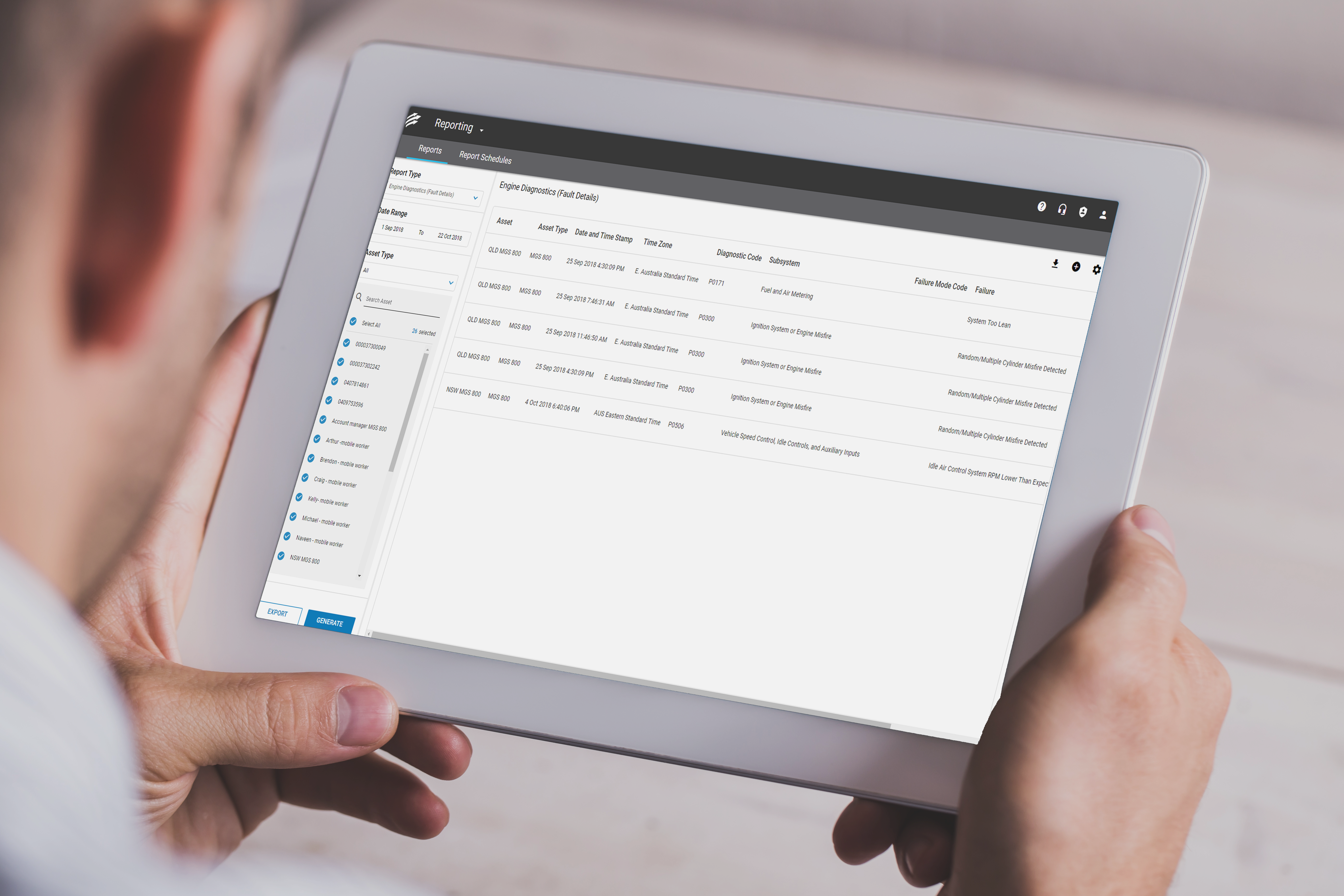
Big Data is transforming fleet management. Telematics can give managers insight into fuel efficiency, driver behaviour, mileage, idling, and more – offering a gold mine of valuable information for your business.
With this information, fleet managers gain measurable, actionable insights that can help them control driver safety, operating expenses, and security at all times.
This data also has to stay protected from hacking threats, especially as cybercrime rates increase. Upstream.auto recently reported a 94% year-on-year rise in cyber attacks on vehicles since 2016.

Cybercrime is reported every 10 minutes in Australia (Image Source).
The smarter our technology is, the more sophisticated attackers become, according to a spokesperson from the Australian Cyber Security Centre:
“While our cyber adversaries are becoming more adept, the likelihood and severity of cyber-attacks is also increasing due to our growing dependence on new information technology platforms and interconnected devices and systems.”
With the risk of cyber attacks increasing, fleets must put extra emphasis on security.
How to Protect Your Fleet Data
While the advantages of telematics and fleet management software far outweigh the risks, it’s important to keep security measures a top priority. Here are some tips for keeping your fleet data secure.
Choose Your Tech Carefully
Not all technology is created equal. Before making a purchase, it’s critical to investigate the hardware’s capabilities and security. Here are some important factors to consider:
- What are the encryption policies?
- How is security validated?
- Will the telematics provider help with installation and configuration?
- Does the provider have professional services available for customisation?
When choosing technology, speak to your staff about their individual needs to ensure the solution will meet everyone’s requirements.
Review Your Internal Security Policies
Security breaches are usually traced back to a preventable weak spot within an organisation. This is why it’s important to educate everyone within the business – including drivers, managers, IT teams, and administrators – about security threats. If everyone understands the risks and consequences, they’ll be more likely to take steps to prevent issues from arising.
Along with training, it’s important to have a clear policy set out that’s communicated and shared among staff. Make sure it’s easily accessible so there is no excuse for slip-ups. Your policy should include the following:
- Communication processes
- Password safety
- How to properly lock up a vehicle
- How to spot threatening behaviour
- Instructions for proper vehicle usage
- Guidelines for data use and system updates
Limit Access
Access to data should be as secure as access to vehicles. In the same way you authorise who can access vehicles, you can also create a list of people who can access data. It should be a short list: ideally just the driver on duty and those higher up the chain of command.
If you have an internal tech team monitoring your data, ensure infrastructure is in place so employees follow best practices, which should be regularly updated and aligned with current regulations.
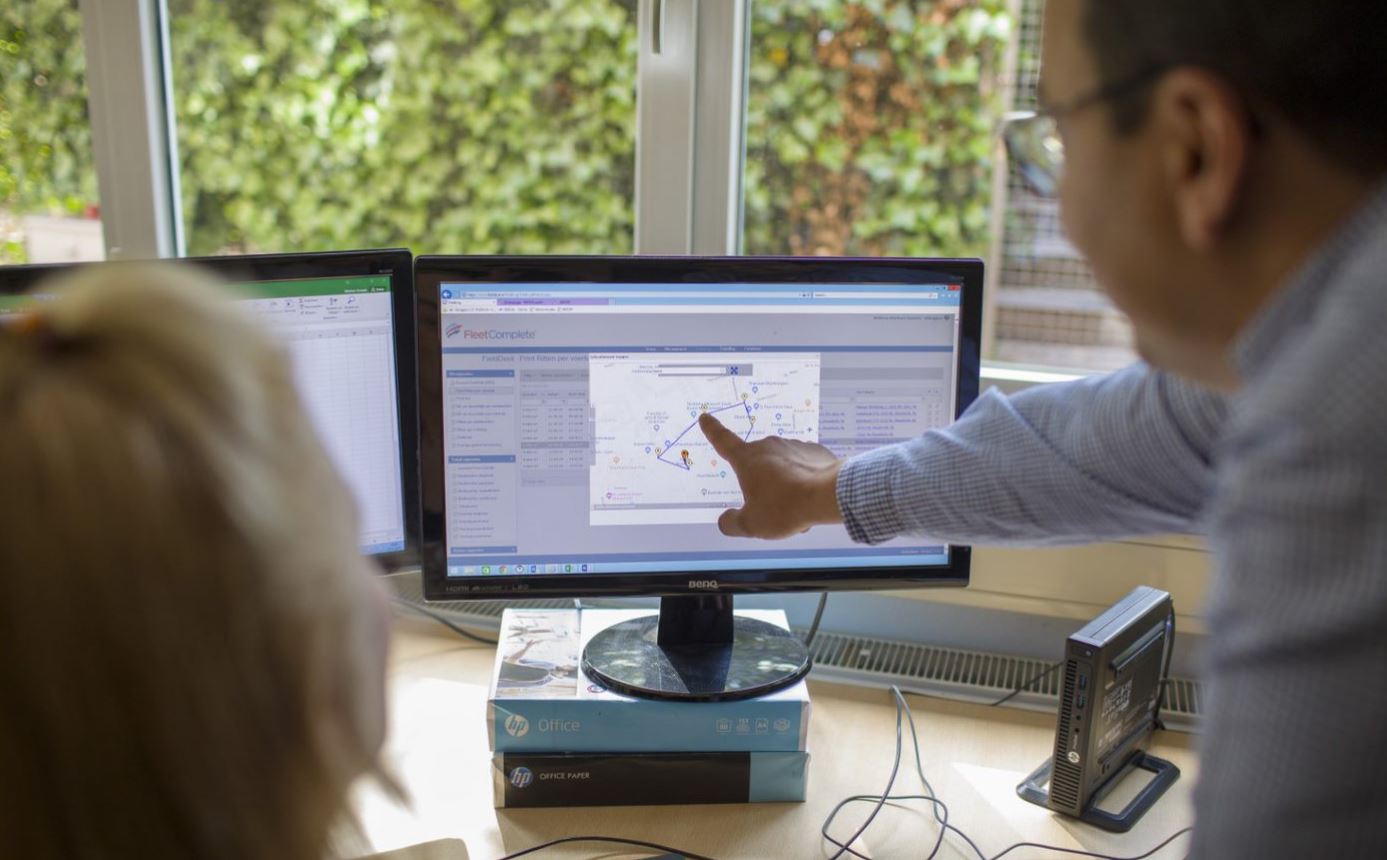
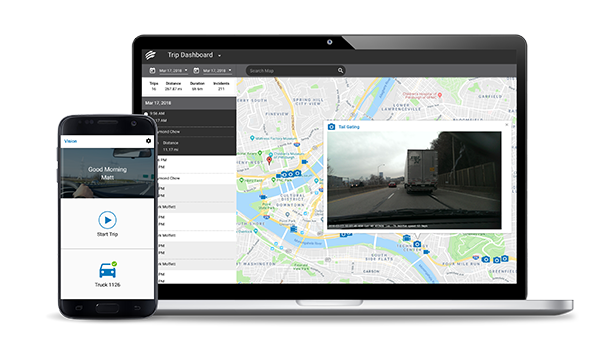
Keep an Eye on Your Notifications
Your software should do most of the heavy lifting for you, but it’s a good idea to keep an eye on suspect issues 24/7. For example, if you spot a vehicle making a big fuel purchase but its GPS says it’s nowhere near a gas station, that could signal a problem. Real-time alerts inform your team quickly so you can act accordingly. Remember: being proactive is always your best course of action.
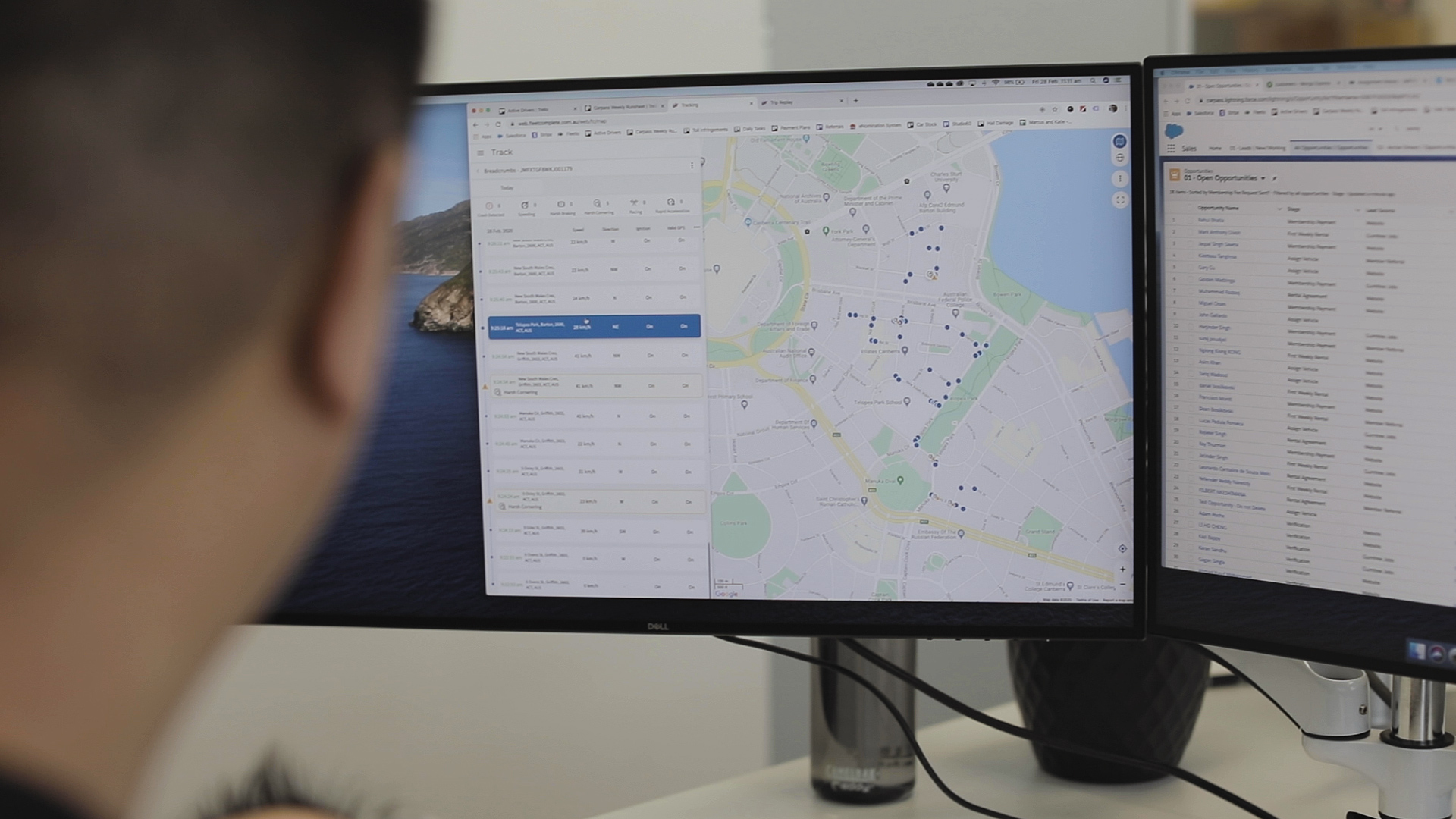
With Fleet Complete’s Fleet Tracker, keeping track of your fleet is no problem, as you’ll receive updates and notifications in real-time – helping to ensure everything is where it’s supposed to be.
![]()
Keep Your Systems Up-to-date
Software updates are there to fix bugs, address vulnerabilities, and add features designed to keep your fleet safe. If you skip an update, not only are you leaving yourself open to threats, your insurance company may also see the failure to update as negligence and refuse to cover you.
Luckily, most software updates automatically. When purchasing technology tools, updates and system improvements are things to keep in mind.
Conclusion
While fleet management technology provides tons of benefits to fleet-owning business, like any tech, it comes with its share of vulnerabilities.
However, by keeping security methods in mind and choosing the right fleet management software for your business, you can help mitigate these concerns and keep your fleet data secure.
With Fleet Complete’s fleet management system, security is always at the top of mind. Take it for a spin to see all the benefits it has to offer and how it can help optimise fleet security. Get started today by trying our Fleet Complete demo.
If you found this article helpful, please share it on social media.